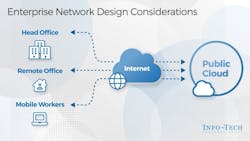
Does remote work require a redesigned enterprise network?
Global IT research and advisory firm Info-Tech Research Group (Toronto) has published its newest research-backed blueprint, entitled Enterprise Network Design Considerations.
(As clarified by a statement on the research firm's website, "A blueprint is designed to be a roadmap, containing a methodology and the tools and templates you need to solve your IT problems." The firm notes that each blueprint can be accompanied by a "guided implementation" which provides access to the firm's analysts to help stakeholders get through a project.)
The firm maintains that the new research is timely, given the growing number of remote users and services provided "off network," which has contributed to a rapid rise in enterprise security threats.
Info-Tech says its new blueprint "will help security and IT leaders develop a network design that considers more than just connectivity to address these concerns, while delivering business value."
An executive summary of the research contends:
Security, risk, and trust models are factors IT teams need to consider when designing and deploying an enterprise network. If these models are not considered during network design, band-aids and workarounds will be deployed to achieve the needed goals, potentially bypassing network controls.
Many enterprises still use traditional networks, which commonly include comprehensive firewalls and dedicated hardware devices such as switches and routers to control data traffic but have limited security.
With the increasing amount of work that the business is completing remotely, not all devices and data paths will be under the control of IT. However, this shift does not allow IT to abdicate from the responsibility to provide a secure network.
In summary, Info-Tech says its research indicates that the cloud "gold rush" has made it attractive for many enterprises to migrate services off the traditional network and into cloud-based services such as inverted perimeter or hybrid networks for better security and connectivity.
Inverted perimeter networks
As defined by the researcher, "an inverted perimeter network is one in which security and control points cover the entire workflow, on or off net, from users to the services themselves, with a zero-trust principle. Since the control plane is designed to encompass the workflow in a secure manner, much of the underlying connectivity can be abstracted."
The firm's research suggests that an inverted perimeter network model is extremely attractive for organizations that primarily consume cloud services and have a large remote workforce.
Hybrid networks
A hybrid network combines elements of a traditional network with cloud resources. The research contends that as some of these resources are not entirely under the control of IT, and may be completely off net or loosely coupled to the on-premises network, the security boundaries and control points are less likely to be centralized.
The blueprint finds that hybrid networks allow the flexibility and speed of cloud deployment without leaving behind traditional network constructs, but are generally more costly to secure and maintain.
Info-Tech recommends security and IT leaders understand the needs of the business before choosing a network design for the organization. The blueprint highlights certain factors that should be considered when trying to understand business needs, which as stated by Info-Tech include:
- Mission: Consider the mission and vision of the business to address relevant needs.
- Users: Identify where users will be accessing services; Remote vs. "on net" is a design consideration now more than ever.
- Resources: Identify the required resources and their locations i.e. on net vs. cloud.
- Controls: Identify the required controls in order to define control points and solutions.
"A network archetype needs to be defined to understand what tools are appropriate for consideration in a network build or refresh," notes Scott Young, principal research advisor in Info-Tech's Infrastructure Research Practice. "These tools, which are purpose-built and generally designed to solve specific problems, must be chosen appropriately to align with the organization's challenge."
The new research blueprint also contains insights and direction for IT leaders on other key topics, such as archetypes and tooling, hybrid and inverted networks, and cloud access security brokers (CASB) and secure access service edge (SASE).
Download and view the complete 'Enterprise Network Design Considerations' blueprint from Info-Tech Research.
For more news, projects, and profiles in the ICT cabling and connectivity industry, subscribe to CI&M’s newsletter and follow us on LinkedIn, Twitter, and Facebook.
About the Author
Matt Vincent
Senior Editor
Matt Vincent is a B2B technology journalist, editor and content producer with over 15 years of experience, specializing in the full range of media content production and management, as well as SEO and social media engagement best practices, for both Cabling Installation & Maintenance magazine and its website CablingInstall.com. He currently provides trade show, company, executive and field technology trend coverage for the ICT structured cabling, telecommunications networking, data center, IP physical security, and professional AV vertical market segments. Email: [email protected]