10 tips for Industrial Ethernet/IP deployments
Industrial managers seeking to deploy plantwide Ethernet/IP technologies might refer to these 10 design recommendations for industrial networks, as outlined in an evergreen technical brief (published in 2011) from Rockwell Automation and Cisco:
1. Understand a networked device’s application and functional requirements: These include data requirements such as communication patterns and traffic types (i.e. industrial and non-industrial).
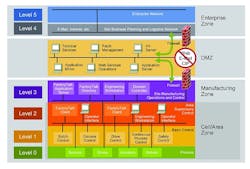
2. Enable a future-ready network design: Use industry and technology standards, reference models and reference architectures (such as Cisco and Rockwell Automation's Converged Plantwide Ethernet (CPwE) Architectures).
3. Create structure within the plantwide Ethernet/IP network: Develop a logical topology that uses both a multi-tier switch hierarchy (Layer 2 and Layer 3) and the logical model shown in the figure below. Define zones and segmentation, then place industrial automation and
control system devices, servers or other communicating end-devices within the logical topology based on their location, function, availability and performance requirements.
To design and plan a plantwide Ethernet/IP network, first consider each level of the logical model shown here.
4. Segment the logical topology into modular building blocks: Create smaller Layer 2 networks to minimize broadcast domains. Use virtual local area networks (VLANs) within a zone to segment different traffic types, such as industrial and nonindustrial. Minimize the number of devices to less than 200 within a zone and VLAN. Use firewalls to strongly segment the manufacturing and enterprise zones, creating a demilitarized zone (DMZ) that enables secure sharing of applications and data between the zones.
5. Use managed industrial switches: These provide key network services such as loop prevention, resiliency, segmentation, prioritization, time synchronization, multicast management, security and diagnostics.
6. Design and implement a robust physical layer reflecting availability and resiliency requirements: Overlay the logical topology over the plant physical layout to create the physical topology. Use 1 gigabit-per-second fiber uplinks and redundant paths between
switches for optimal network resiliency. Ensure the end devices and network infrastructure devices communicate at the best possible speed and duplex. Deploy physical cabling corresponding to plant conditions and requirements. In addition, deploy a defense-in-depth approach to help prevent noise coupling through techniques such as bonding, EMI segregation, shield barriers and filtering.
7. Determine application and network security requirements: Establish early dialogue with IT, considering applicable IT requirements. Implement a defense-in-depth security approach at multiple application layers such as physical, device, network and application, using an industrial security policy that’s unique from and in addition to the enterprise security policy.
8. Reduce network latency and jitter by using standard network protocols: Protocols include time synchronization using IEEE 1588 precision time protocol (PTP), quality of service (QoS) for control data prioritization and Internet Group Management Protocol for multicast management.
9. Increase control and information data availability: Implement a redundant path network topology such as a ring or redundant star. In addition, use a resiliency protocol to avoid Layer 2 loops while helping to ensure fast network convergence time. These considerations affect how quickly the network will recover from a disruption, which may result in application timeouts and system shutdowns.
10. Deploy a hierarchical network model using Layer 3 switches: Layer 3 switches support inter-VLAN routing between cell/area (Layer 2 network) zones and plantwide applications and servers. Layer 3 switch capabilities enable design recommendation #4. If the application requires industrialized Layer 3 switches, consider products such as the Allen-Bradley Stratix 8300 Layer 3 managed switch.
View/Download the full technical brief from Cisco and Rockwell Automation